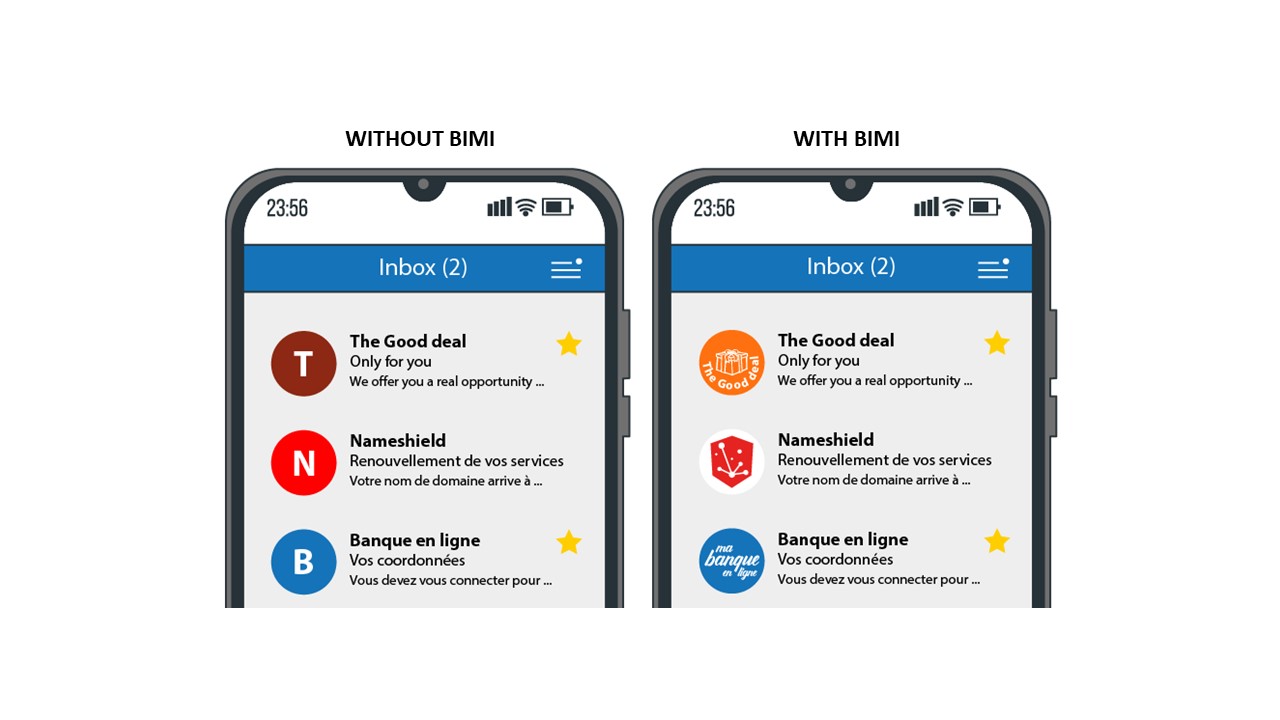
BIMI (Brand Indicators for Message Identification) allows you to authenticate your emails and reinforce the trust of your customers by displaying your logo in their inbox. VMC (Verified Mark Certificate) is a certificate associated with BIMI, which ensures the authenticity of the logo displayed.
What is BIMI?
BIMI is an industry initiative aimed at standardizing the use and display of brand logos in email clients. By placing a brand or company logo next to an email, it is more easily identifiable by customers and users, builds a sense of legitimacy and trust, significantly impacts open rates, and increases consumer protection against fraudulent emails.
Technically speaking, BIMI is an emerging security technology that works alongside DKIM, SPF and DMARC protocols to protect your domain name from being used by malicious actors to send fraudulent emails.
Before BIMI, the steps to get your logo next to an email were specific to each email service your message was sent to. Sometimes the process was entirely manual or relied on other applications to aggregate your brand information and share it across participating platforms.
The AuthIndicators group, which includes email service providers such as Google, Verizon Media, IONOS by 1&1 and Fastmail, is working to implement BIMI in the most common email clients. Many players have already adopted BIMI, others are in the process, Microsoft’s and Apple’s positions are expected to drive final adoption of the standard.
Why is BIMI important?
To complete the arsenal of a brand’s protection on the Internet, more specifically against hijacking attempts through fraudulent spoofing emails whose goal is to deceive the user and lead them to phishing sites.
306 billion emails circulated worldwide in 2020, with an ever-increasing proportion of fraudulent emails hijacking brands.
To increase the desirability of emails, particularly in marketing campaigns. The implementation of BIMI and more widely of security protocols and certificates on the domain name associated with a brand is essential today and has a major impact on online reputation.
Because it is becoming a market standard, easy to implement unlike the number of existing anti-fraud email solutions that are often difficult to test and implement.
How does BIMI work?
BIMI uses a process of several steps to validate emails by ensuring that they are actually associated with the sender’s domain name. Senders must add a TXT DNS record dedicated to BIMI.
For BIMI to work, domain names must also have several other fraud protections, including:
- SPF (Sender Policy Framework): authenticates emails by identifying mail servers authorized to send from specific domain names ;
- DKIM (DomainKeys Identified Mail): adds a digital signature to each email to verify that it was sent from an authorized domain name;
- DMARC (Domain-Based Message Authentication, Reporting, and Conformance): confirms SPF and DKIM records and specifies how non-compliant emails should be handled.
When emails are sent using BIMI, the receiving mail server will first do the standard DMARC/DKIM authentication and SPF validation. If the email passes these checks, the mail server will verify that it has a valid BIMI record and display the brand logo.
How does BIMI interact with DMARC, DKIM and SPF?
The first step towards using BIMI to display a logo is to implement DMARC. This is stored as a DNS record of TXT type on the domain name. For DMARC to work with BIMI, the reject policy in this record must be p=quarantine or p=reject for all emails sent from your domain.
BIMI requires DMARC… and DMARC requires your domain name to have DKIM records to work. While DMARC only requires SPF or DKIM to work, it is best to include SPF records for more security when using BIMI. These 2 security tools are also stored as TXT DNS records in the domain name zone.
VMC, the final link in the chain
A Verified Mark Certificate is a digital certificate that authenticates the ownership of a logo, and completes the use of BIMI in email clients such as Gmail.
The VMC certificate guarantees the authenticity of the logo displayed, which is necessarily owned by the domain name holder sending the email. It is the last link in the chain to guarantee the authenticity of the email received.
When you send an email to a contact, the receiving mail server that manages their inbox will take the URL of the tag that indicates where the logo should be displayed. It will then check the VMC certificate to ensure that the correct logo is used. Once the logo is verified by the VMC, BIMI will display it next to the email in the inbox.
To obtain a VMC certificate, the implementation of DMARC on the domain name is a prerequisite. Then follows a reinforced authentication process with a Certification Authority that will validate the identity of the Organization, the registration of the logo with a certified body and will issue the certificate after a one to one meeting with a notary.
Depending on the country, the intellectual property offices for logos registrations may vary as well as the rules of acceptance to issue the certificate. The notions to keep in mind, the authorized trademarks can be:
- Design trademarks: consist exclusively of a design;
- Verbal trademarks: contain words, letters and/or numbers, without any particular font, size, color or style;
- Combination trademarks: include a combination of words with a design, stylized letters or numbers.
While this is not a requirement for implementing BIMI on your domain name at this time, VMC should be part of the standard in the future.
Entrust Datacard and DigiCert are the first 2 companies to issue VMC certificates for the BIMI standard. Nameshield is a partner of both companies and will assist you in obtaining VMC certificates. You can contact directly our certificates department for any question on the subject.
BIMI + VMC = Guarantee of authenticity
BIMI, VMC… and Nameshield
Nameshield now assists its customers in all aspects of the implementation of DMARC, SPF, DKIM, but also BIMI protocols and the obtaining of associated VMC certificates. The domain name is at the core of the implementation of these different protocols. Our historical business as a registrar and DNS zones manager allows us today to assist our customers on these major subjects of the fight against online fraud and the increase of emails desirability.