Although ICANN regularly visits Asia, we have to go back to ICANN 57 exactly 10 years ago to find India as the host country for an ICANN Summit. Following Hyderabad in 2016, it was the financial capital, Mumbai, that hosted the 85th ICANN Summit from 7 to 12 March. A summit taking place just seven weeks before the opening of the new application window for new extensions, but also against the backdrop of a geopolitical landscape that has once again been thrown into turmoil, one week after the start of military strikes in Iran and Lebanon.
Participation remains strong despite the geopolitical context
ICANN reported 1,407 on-site attendees from 112 countries, a figure close to the typical attendance levels at the organization’s first annual summits. Nevertheless, there was a sense that the rooms hosting the 200 sessions seemed less crowded than usual. The impact of the military intervention in Iran on affected air routes throughout the region likely played a role in this. Many participants reported having to opt for remote or abbreviated participation due to flight uncertainties.
A Welcome ceremony that balances solemnity with a focus on the work ahead
ICANN Board Chair, Tripti Sinha reminded attendees at the opening ceremony that she was born in the state of Maharashtra, of which Mumbai is the capital. She addressed the global situation, noting that ICANN85 is taking place “during a time of profound suffering.” But she also emphasized that what unites us is stronger, citing a Sanskrit proverb: “The world is one family,” which echoes ICANN’s slogan: “One World, One Internet.”
For Tripti, this week was to focus on three main topics:
- The conclusion of the WSIS+20 review, which recognizes the role of multistakeholder internet governance;
- Accountability and transparency, with ICANN’s new holistic review currently underway;
- And the launch of the new round of applications for internet extensions.
On this last point, she noted that it is “the culmination of years of work.”
Kurtis Lindqvist, ICANN’s CEO, added to these topics the ongoing work to establish binding deadlines for urgent requests for access to domain name registration data and authentication technologies, as well as the progress still needed regarding DNS abuse.
Detailed timeline for the next round unveiled
Eight thematic and operational sessions were dedicated to the next round of new top-level domains. What are the key takeaways?
ICANN85 first confirmed the major upcoming milestones of the program as well as the proposed dates.
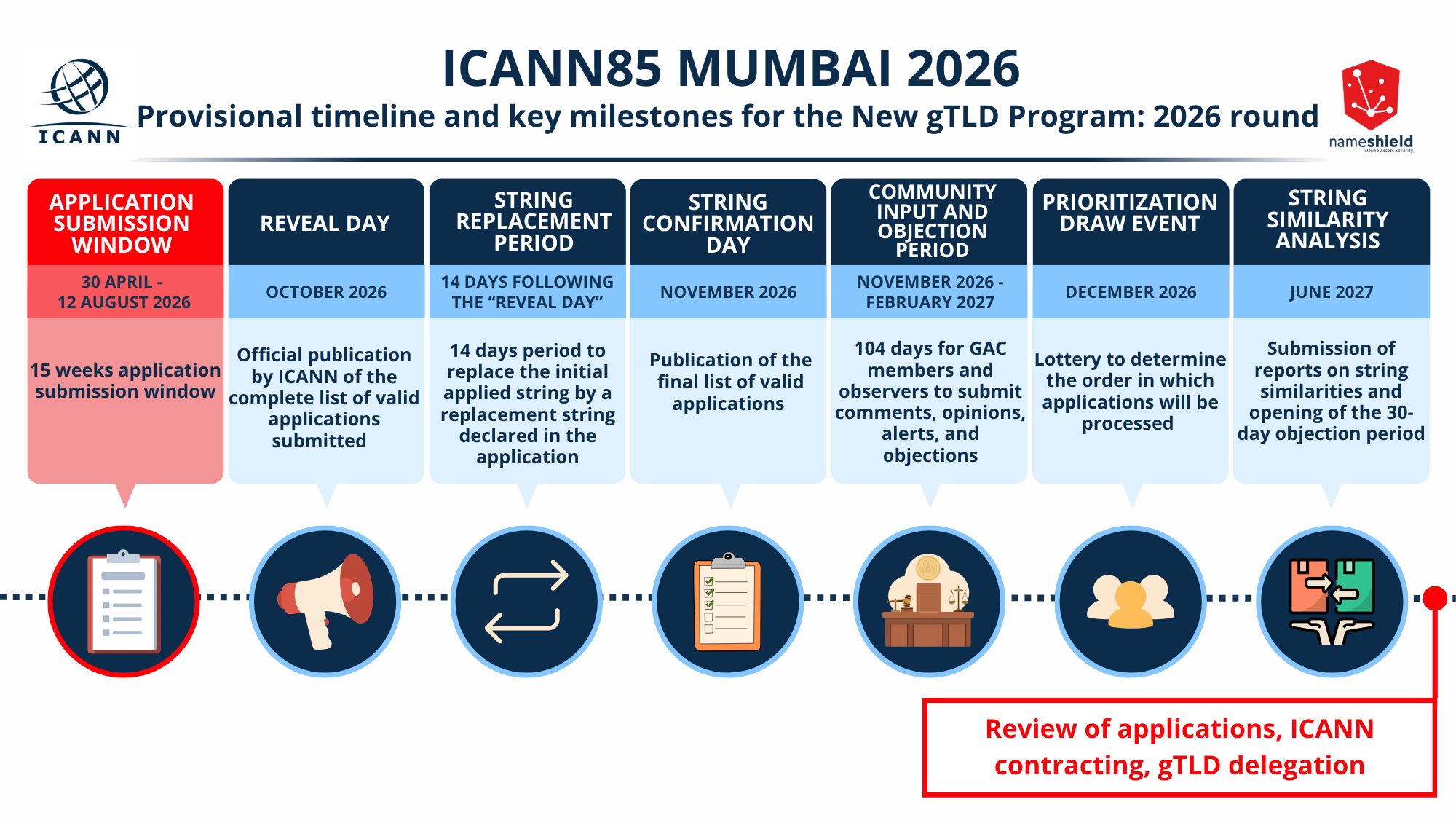
April 30 to August 12, 2026: Application submission window
Until early October 2026: ICANN administrative review period for applications
Mid-October: “Reveal Day”. It is the official publication by ICANN of the complete list of valid applications submitted for new extensions.
Until early November: Replacement string period. This is a new mechanism that allows applicants who have applied for the same extension or extensions deemed similar to replace their initial string by a replacement string declared in their application. Applicants for dot brand extensions may choose to add a term to their brand that corresponds to the goods and services declared in their registered trademark. The substitution window is expected to last 14 days. ICANN hopes this will reduce disputes between applicants seeking identical or overly similar extensions.
Mid-November: “String Confirmation Day”. ICANN will publish the official and final list of applications for new top-level domains.
November 2026 – February 2027 (104 days): Community input and objection period. This period allows members of the GAC—the body representing governments—and observers to submit comments, opinions, alerts, and objections.
At the same time, in mid-December, ICANN plans to hold a Priority Draw Event, a lottery to determine the order in which applications will be processed during the evaluation phase. This process was also used during the 2012 round.
June 2027: Deadline for the submission of reports by an evaluation panel on string similarities among the submitted applications and in relation to existing extensions. A 30-day objection period will be opened to challenge a candidate string if it creates confusion with another extension.
Starting in the second half of 2027: Dispute resolution is expected to follow, along with the review of applications to move toward contractualization and integration into the DNS root, the long-awaited delegation of the first extensions.
ICANN emphasized that these dates remain subject to change, particularly depending on the volume of applications that are submitted. ICANN has nevertheless indicated that it has sufficient capacity to handle a volume of applications similar to that of the 2012 round, or nearly 2,000 applications.
The latest tools for the next round are finally known
Among the two major elements still to be confirmed for the next round are the application submission tool and the ICANN contract for future registry operators seeking to participate.
To the 2012 TAS (TLD Application System), we must now add the letter « M ». TAMS (TLD Application Management System) indeed is the name of the new portal ICANN has developed to manage applications during the 2026 round. This portal, unveiled late in the process, is currently in the testing phase, particularly to assess its robustness. Some participants expressed regrets that it was unveiled so late and that it lacks certain helpful features, such as the ability to export data.
The new registry agreement, another key element for future registry operators, reached a conclusion with its approval during the public session of the ICANN Board of Directors, which is traditionally held at the close of the summit.
The geopolitical context and DNS abuse were discussed throughout ICANN85
Whether through targeted sessions or questions from participants during Q&A slots, geopolitical issues also came up at ICANN 85. Following the Opening Ceremony, ICANN scheduled a session titled: “From Stability to Survivability: ICANN’s Role in the Future of Internet Resilience.” During this participatory session, ICANN sought to examine how the DNS ecosystem can withstand global systemic failures that would affect the cloud, energy supply, the digital supply chain, and software dependencies. For example, the session revealed that for 38% of participants, ICANN’s main blind spot is cross-sector coordination—specifically communication with the energy, telecommunications, and finance sectors, areas over which the organization has no control. Second, respondents cited ICANN’s difficulty in ensuring operational compliance among registries and registrars under global conditions that would have become extremely challenging.
Regarding DNS abuse—a topic that has also come up repeatedly—a mixed assessment was made of the impact of the contractual amendments introduced over the past two years for registry operators and registrars. ICANN85 marked the operational launch of a first new policy development process to work on « Associated Domain Checks », a mechanism that would require registrars to verify other domain names linked to the same registrant when a domain is identified as malicious. Its goal is to identify networks of domains used for activities such as phishing, botnets, or malware and to act more quickly against coordinated campaigns.
With less than five weeks to go before the application window for the next round opens, now is a good time to remind everyone that applying for an internet domain extension—particularly .brand—requires advance planning, as time is now running out. We’re already in the final sprint. Should you apply or not? Which extension should you pursue, and what alternative string should you consider, if necessary? Who should you contact to help gather the materials for the application? What budgets should you rely on to cover the application process? In just over four months, the window will indeed already close, yet an application requires preparation to cover the 225 sub-sections of the application and meet tight deadlines.
Nameshield offers a turnkey and tailored approach to simplify all your steps as much as possible, meet deadlines, track your application from start to finish to bring it to the contract stage and then integration into the global DNS root, and subsequently provide you with all the expertise to maximize its benefits while ensuring its long-term contractual and regulatory compliance. If there’s one tip to take away from ICANN85 regarding the next round: “Don’t wait until the last minute.” Take action now by entrusting your project to us.