Or how to benefit from it to implement a certification strategy specific to your company?

In January 2013, a new type of DNS Resource Record has appeared to improve the control chain in the SSL certificates issuing. This record, called CAA for Certificate Authority Authorization, allows to specify for a given domain name which Certification Authorities are authorized to issue certificates.
It’s an extremely interesting creation, in particular for big companies and groups, which technical teams are scattered in the World and for which it’s often difficult to require a global certification strategy. It’s not unusual for companies to accidentally discover the existence of certificates requested by teams not knowing the processes, by external consultants, issued by Certification Authorities with a bad image, or for certificates of low level of authentication (DV). The implementation of CAA record on your domain names is a good solution to control what the teams are doing and the news on SSL’s world will help you do that.
Indeed, if the CAA has been detailed in the RFC-6844 from 2013, it was not mandatory until today, for a Certification Authority to check if it was authorized or not to issue a certificate on a given domain name, hence a certain uselessness of this and a very low adoption.
September 8th, 2017 – The CAA checking becomes mandatory
We had to wait until March 2017, and a positive vote of the CAB/forum (ballot 187) to make this verification mandatory. Since the 8 September, the Certification Authorities have the duty to do this verification at the risk of sanctions from CAB/forum and browsers, the recent news regarding Google and Symantec has shown us how it’s not in their interests.
Three scenarios occur during this verification on a given domain name:
- A CAA record is set and indicates the Certification Authority name, this one can issue the certificate.
- A CAA record is set and indicates a Certification Authority’s name different, this one CANNOT issue the certificate.
- No CAA record is set, any Certification Authority can issue a SSL certificate.
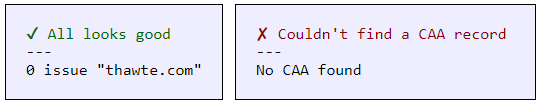
It’s important to note that for a given domain name, many CAA records can be declared. A simple tool (among many others) to test your domain name, is available online: https://caatest.co.uk/
How to benefit from CAA for my company?
If it’s not already done, the establishment of the CAA checking is the opportunity for your company to define a certification strategy and to be able to ensure that it is complied with.
Define one (or multiple) Certification Authority corresponding to your values and to your expectations in term of service quality is a first step.
It will require to put around the table the marketing stakeholders to validate the impact on websites display and the technical services to ensure of the chosen provider’s quality. It will then be necessary to declare these CAA records in the different zones of your domain names.
It’s then important to communicate with all the operational staff so they become aware of the rules imposed within the company, in order not to block them in obtaining a certificate.
Indeed, Nameshield’s experience shows that SSL certificates are often requested in a hurry; moreover the browser’s last versions are not kind towards certificates’ errors by ostensibly displaying “not secure”. In consequence, blocking the issuing of a certificate because the communication didn’t get through can be damaging.
Such strategy presents real advantages in the control of certificates, in marketing, technical, risks control and costs associated to certificates. It’s necessary to conduct it with full knowledge and in order to do it, our SSL experts’ team can assist you.

