DNSSEC has taken shape, and has become essential in security process recommended by ANSSI as well as the web in general. And yet, it’s a barbaric term that is often scary as we don’t know how it works and what it’s used for. This article will focus on clarifying this term.
The Domain Name System Security Extensions is a standardized protocol of communication allowing to resolve security problems related to DNS. We will begin by a reminder of what is the DNS.
What is the DNS?
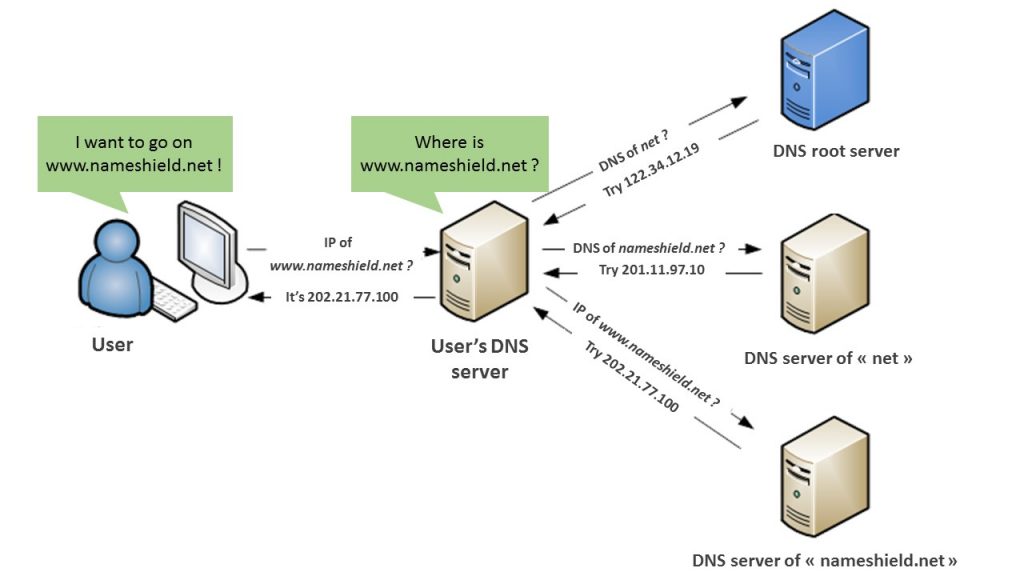
Simply put, the Domain Name System is quite like an Internet directory. It’s a service translating a domain name into IP addresses. It relies on a data base distributed to millions of machines. Humans identify, memorize and differentiate more easily names than series of numbers. The DNS has been defined and implemented in the 80’s and has become an essential element of Internet.
How does the DNS work?
The DNS will allow web user to inform a domain name in his web browser to access a website. The browser will then “resolve” this domain name to obtain the IP address of the web server which hosts this website and displays it. We call this the “DNS resolution”.
What are the risks related to the DNS?
If the DNS goes down, your websites and emails are going to be unavailable, which is unthinkable nowadays. Other applications can be impacted in the companies: VPN access, intranet, cloud, VOIP… all that potentially needs a names resolution to IP addresses. DNS must be protected and stay highly available.
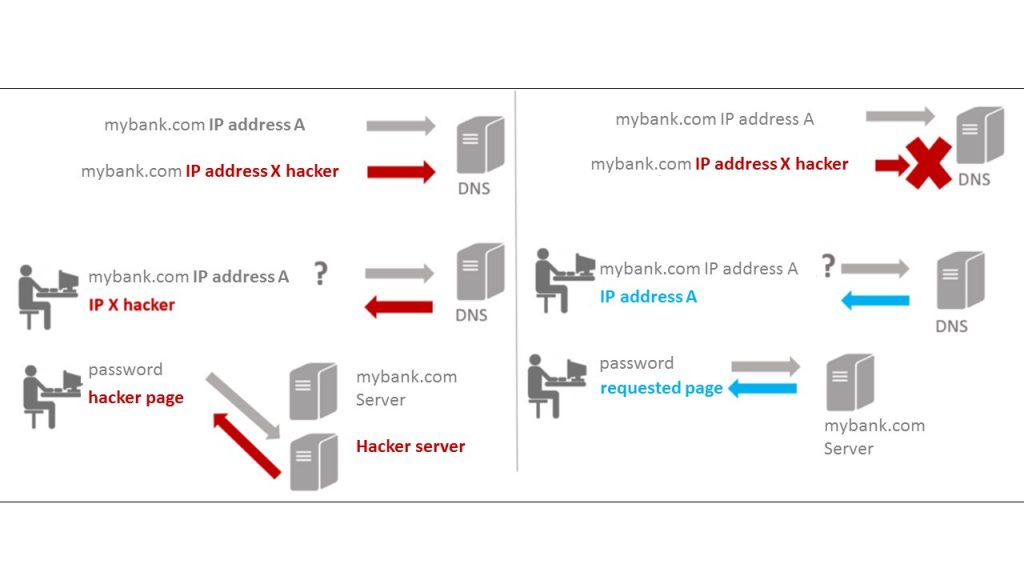
If the DNS protocol has been created with security in mind, many security flaws of the DNS protocol have been identified since its creation. The mainly flaws of DNS have been described in the RFC 3833 published in August 2004. Queries package interception, fake answer, data corruption, DNS cache poisoning and Denial of service.
To deal with this vulnerability, DNSSEC protocol has been created.
DNSSEC issues
DNSSEC prevents these different attacks, particularly cache poisoning, by securing the integrity of the DNS resolution. DNSSEC issues are:
- How to secure the data integrity and authenticate DNS (resolver, server with authority) and keep backward compatibility with the DNS at the same time.
- How to secure access security at the resource asked to billions web users?
- How to find a solution light enough so it won’t surcharge names servers?
DNSSEC process
To secure the integrity of the DNS resolution, DNSSEC develops a chain of trust that goes back to the DNS root (refer to the DNS root server image above). Data security is done by keys mechanism (KSK for Key Signing Key & ZSK for Zone Signing Key) which signs DNS records in its own zone. Public keys are sent to the corresponding register to be archived; the register being linked by DNSSEC to the root server, the chain of trust is developed. Each DNS parent zone ensures the keys authenticity of its child zones by signing them.
Without DNSSEC With DNSSEC
DNSSEC, Nameshield and you:
DNSSEC operates like an essential protection for your strategic names, which secures DNS’ answer authenticity. It would be advisable to identify names that need to be protected. All TLDs don’t propose DNSSEC yet. Here is a list of principal TLDs that does, it can change with many more coming:
TLDs supporting DNSSEC: .fr, .com, .be, .net, .eu, .pl, .re, .pm, .yt, .wf, .tf, .info, .li, .ch, .biz, .de, .sx, .org, .se, .nl, .in, .us, .at, .nu, .la, .ac, .cz, .me, .sh, .io, .uk, .co.uk, .me.uk, .org.uk.
All news gTLDs, like .paris, .club, .xyz, .wiki, .ink, support also DNSSEC.
DNSSEC is included without supplement in Nameshield DNS Premium offer. Nameshield supports you in this process to secure your immaterial assets and manages the integrality of the DNSSEC protocol for you, from keys creation, to storage and renewal.
It’s not the only answer to set, registry lock system, DNS Premium service, SSL certificates are complementary solutions to implement, we will have the opportunity to discuss it in other articles or in the next nameshield.cafe.